
Introduction
In this blog series i will highlight some technical aspects about creating and managing security layer by code in Dynamics 365 For Finance and Operations, a step by step scenario to explain some components used in standard mechanisms to generate new security artifacts through x++, deep dive into Dynamics security management API and discover more in details how to use it.
The Agile FinOps security in Dynamics 365
For me when i say FinOps, i think always about a new way of Financial management solutions, a model based on the total integration of cloud solutions, as an economic and strategic lever for the company and all project stakeholders. But also a model that places all members of the organization in a context of continuous sharing of financial information through daily real-time reports, automated resources and fast and efficient feedback loops.
This centralization of teams around business processes and financial operations in a cloud environment will only improve the efficiency and daily innovation of project members, if and only if security is placed at the heart of this model and plays an important role in governance and defined controls for the use of the cloud for each user in this system.
That’s why choosing the right security implementation strategy at the enterprise level is essential to have an adapated control to different business scenarios and processes, through the definition of a global security policy that cover all roles and permissions, user identities, data and the underlying infrastructure associated to each user in the system.
A recap on GDPR in Dynamics 365 For Finance and Operations

What make every system agile is it’s capacity to be adapated, and easily modified, to meet the customer and business needs, but more than this it must be designed to anticipate the future demand. The challenge that was taken up by Microsoft to make D365 FinOps apps fully compatible with global GDPR rules on different levels of:
- Compliance with data requests
- Asset classifications integration in table fields, can be changed depending on the need to identifiy different type of data
- Consents procedures
- Data control restrictions
- Audit and storage
- Possibility to define new security roles with access to manage sensitive data
- User log integration
- Each organizatoin can define it’s sensitive data : HR, Personal, Financial data.. etc
- Comprehensive search functionality for users
- Person search report integration

Complementary approaches :
Dynamics 365 For Finance and Operations has an array of standard tools and options to help create, configure and modify user roles and manage data security levels through two complementary approaches :
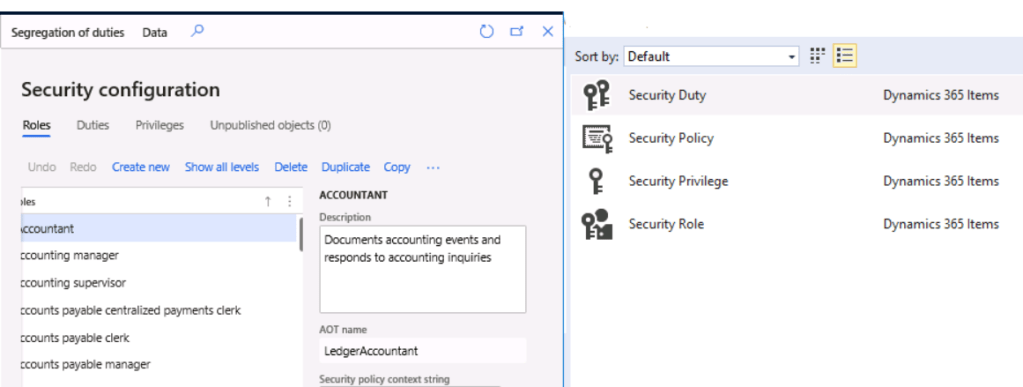
- User Interface: Via « Security configuration » form to configure and manage privileges/duties/roles associations, and role auditing.
- Security diagnostics: Access to see all security diagnostics related to each page in the system, and show associated AOT identifier, with possibility to assign the security diagnostics to any user from this page (no need to go system administration module like AX 2012)

- Visual Studio: If you have technical background you can use Visual studio, and access to the AOT to create and manage new security objects, or use Addins for each form / or via dynamics365 Menu :
- View related roles for all duties
- View related objects and licences for all roles
- View related objects
- View related roles

D365 FinOps application authorization subsystem
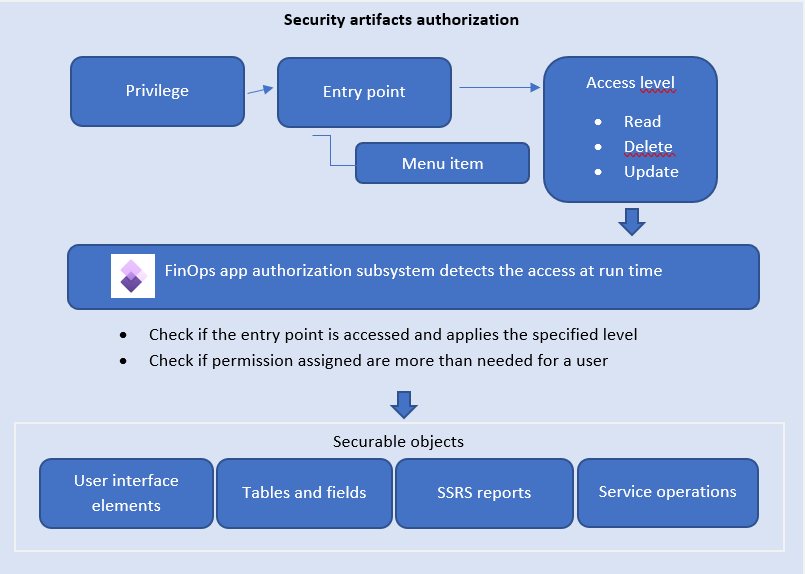
Dynamics 365 For Finance and Operations uses context Role-based security structure which means all users are assigned to roles on a hierarchical way when each element (Role, Privilege, Duty) represent a different level of detail (or part of) in a global business process and the user role is the high level in this structure.
The security of this structure done via authorizing access to individual securable objects in Finance and Operations application by defining specific entry points to privileges with an access level : menu, menu items, action and command buttons, reports, service operations, web URL menu items, web controles, and fields.
Security customization data management
In addition to tables where all security modification and references resides, the application allows data portability to import and export security customized data.
Accessible through « Security Configuration > Data > Export » option
All Security changes in the application can be found in a global XML file that contains all security artifacts changes.

- You can view my blog posts about security data management :
In this first blog post and in order to generate new security artifacts, through this section i will highlight only the main components used in standard mechanisms to start generating new security artifcats, let’s start by the basics.
SysSecurity : Security class
SysSecurity system application class help to manage multiple security operations among them i can mention :
- Managing security repository instances
- Managing Import / Expot data security operations
- Call and manage Microsoft cloud services via Microsoft Graph
- Re-compute menu item role licences associated to security repository for published roles
What is security repository ?
The security repository plays the role of a global data security interaction model which contains all security objects (Roles / Duties / Privileges)

Which information i can get from security repository ?
Using security API, providing a 360° view about security objects through x++ would be handy in some scenarios to get multiple informations about roles, duties or privileges metadata.
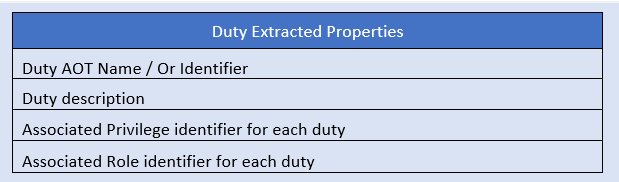
In the following table i summarize most of the AOT properties associated to each security object (Role/ Duty/ Privilege) i can extract from the security repository.
Debbuging « WarehouseManager » role
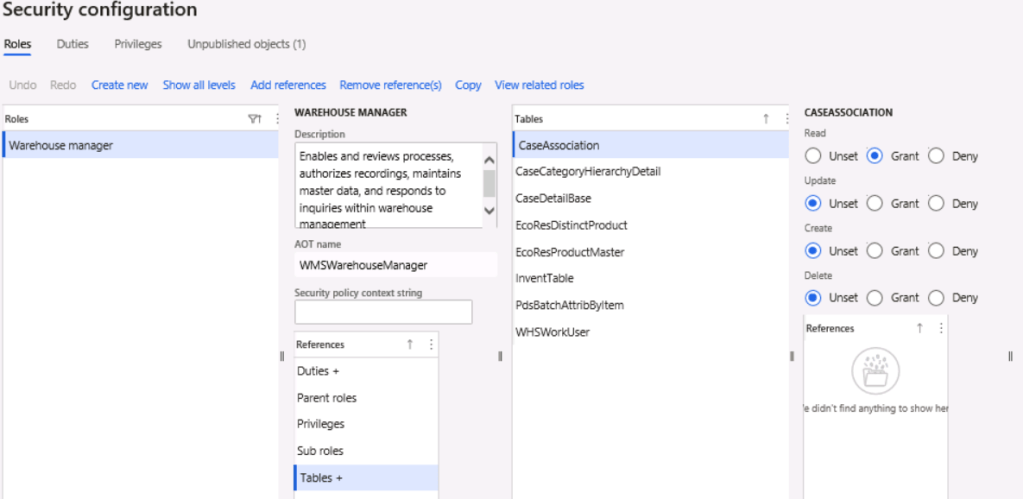
In the debbugger mode, i can access to all associated AOT properties i mentioned above, for example here i’m using WarehouseManage security role, which have 8 table as permissions.

There is more..
In the next blog, i will continue to explain more in details how we can manipulate this security repository with other class interfaces.


Un commentaire sur “Dynamics Security Management API in D365FinOps : part1- Security Generalities”